How To Remove A Hacker From My Phone: Your Guide To Regaining Control
It's a really unsettling feeling, isn't it? That sudden thought, "Is someone else looking at my phone?" Maybe you've noticed some strange things happening, or perhaps a friend mentioned something odd. The idea of a hacker on your phone, well, that's a big concern for anyone. It feels like your private world is, you know, being invaded. This guide is here to help you figure out what to do, actually, if you suspect your phone has been compromised.
A question often asked is how to remove unwanted elements from our digital lives, like those extra Google accounts on a sign-in page or even the Gemini AI if it feels intrusive. But when it comes to a hacker, the stakes are, you know, much higher. It’s not just about deleting an app; it’s about protecting your personal information, your pictures, your messages, and your peace of mind. You might feel a bit violated, like your constitutional right to privacy is, in a way, being stepped on, which is totally understandable.
This article will walk you through the steps to identify, remove, and then secure your device after a potential intrusion. We'll talk about what signs to look for, what actions to take immediately, and how to prevent future attacks. So, you know, let's get your phone back to being just yours, and nobody else's.
Table of Contents
- Signs Your Phone Might Be Compromised
- Immediate Steps to Take When You Suspect a Hack
- Removing the Intruder: Practical Steps
- Securing Your Phone After a Hack: Long-Term Protection
- What If Personal Content Is Exposed?
- Frequently Asked Questions About Phone Hacking
- Taking Back Control
Signs Your Phone Might Be Compromised
It's really important to know what to look for if you think someone might have gained access to your phone. There are several clues that could point to an unwanted presence. One common sign is a phone that just runs slower than usual, or perhaps the battery drains, you know, much faster than it should. Apps might crash often, or your device could restart without you telling it to. These are all pretty much indicators of something working hard in the background.
Another indicator is unusual data usage. If your phone bill shows a lot more data being used than you typically consume, that's a red flag. This could mean a hacker is sending information from your phone to their own servers. You might also notice strange pop-ups, new apps you didn't download, or even calls and texts you don't remember sending. Sometimes, like, your phone might feel warm even when you're not using it much, which could indicate background activity. This warmth is a physical sign of your phone doing more work than it should.
Keep an eye out for weird behavior in your accounts, too. Are there emails sent from your account that you didn't write? Or, you know, do you see purchases on your banking app that aren't yours? These are all pretty strong signals that something is, actually, not right. Even if it's just a gut feeling, it's worth checking out, because your privacy is, after all, very important. You might also find it hard to log into accounts that were previously easy to access.
Other subtle signs could include strange noises during phone calls, like echoes or static, which weren't there before. You might also notice your phone screen turning on by itself, or the flashlight activating without your input. Unexpected requests for personal information through pop-ups that look official, but feel off, are also a warning. Basically, you know, anything that deviates from your phone's normal operation deserves a closer look.
Immediate Steps to Take When You Suspect a Hack
If you think
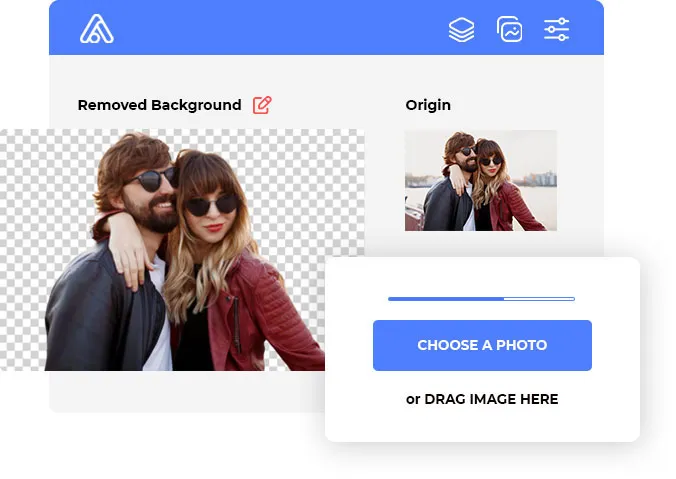
Image Background Remover | Remove BG from Image for Free

Background Remover app for Windows, Mac & Linux –slazzer.com
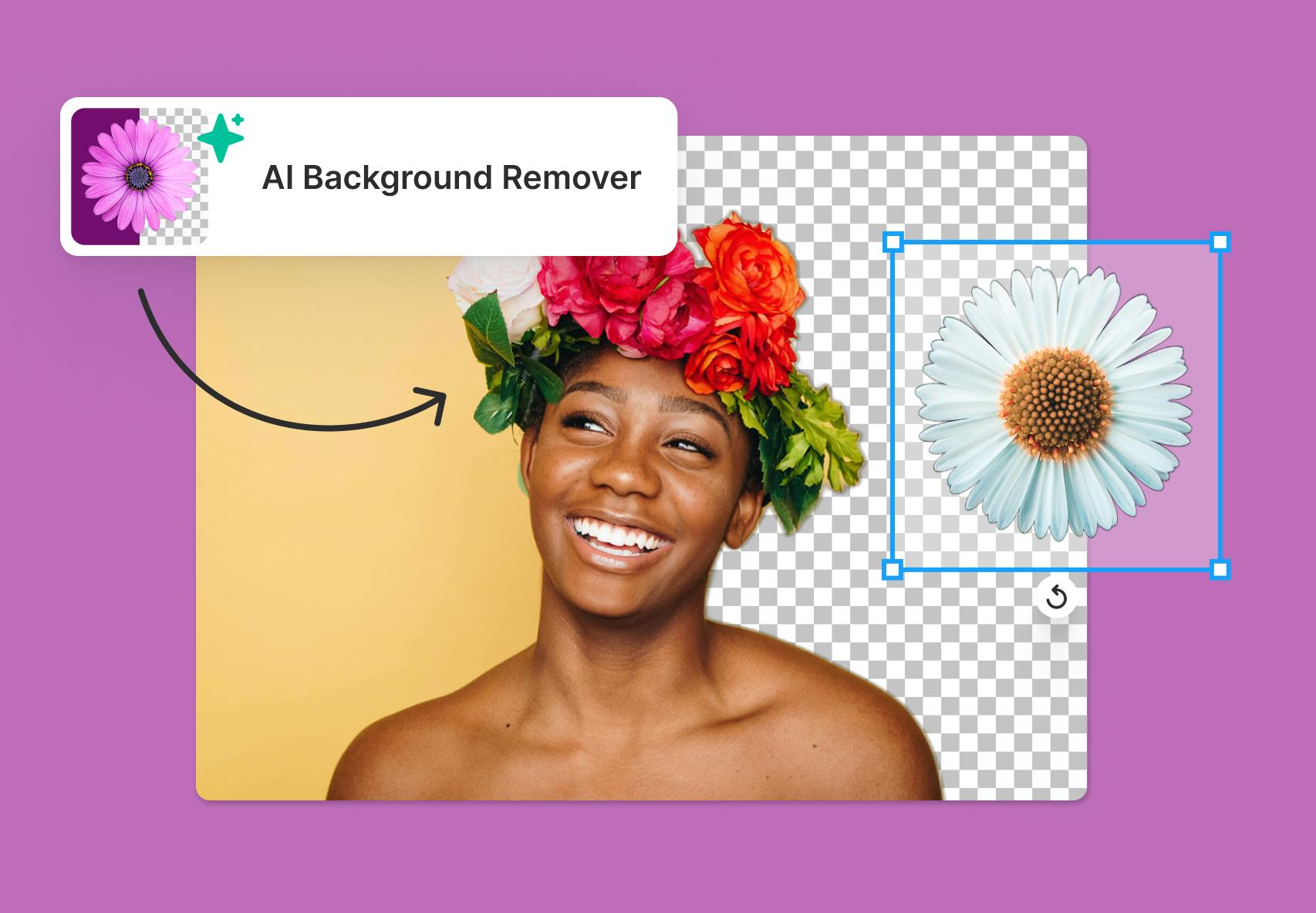
AI background eraser - remove background with AI technology