Understanding When Your IT Administrator Has Limited What You Can Do
Have you ever been in the middle of something important, maybe trying to install a new program or access a specific website, only to be met with a message saying, "Your IT administrator has limited your access"? It can be, you know, a really frustrating moment, stopping you right in your tracks. This message, quite common in today's connected workplaces, often leaves people wondering what exactly is going on and why they can't just do what they need to do.
This kind of message, which, you know, pops up on your screen, is basically a signal that certain actions or areas within your computer system or network are, in a way, restricted. It's not usually a personal thing, actually, but rather a part of how organizations manage their digital tools. We're going to talk about what this message truly means and why it's a regular part of how many companies handle their technology.
So, in this article, we'll try to shed some light on this often-seen phrase, "your IT administrator has limited." We'll look at the reasons behind these limitations, what they typically involve, and, you know, how these rules actually help keep things running smoothly and safely for everyone. It's all about making sense of those digital boundaries, which, you know, are there for a reason.
Table of Contents
- What "Your IT Administrator Has Limited" Really Means
- Common Reasons for IT Limitations
- Types of Restrictions You Might Encounter
- How to Approach IT Limitations
- Frequently Asked Questions About IT Restrictions
What "Your IT Administrator Has Limited" Really Means
When you see that message, it's basically saying that a specific action you're trying to perform, or a resource you're trying to reach, is, you know, not allowed by the rules set up for your computer or network. These rules are put in place by the people who manage the technology, often called IT administrators, and they apply to, you know, your account or the device you're using. It's a way of keeping everything in order, which is pretty important for a big system.
This isn't just about blocking things for no reason; it's, in some respects, a very deliberate choice made to protect the company's information, keep its systems running well, and, you know, make sure everyone is using tools that are safe and approved. Think of it like a building having certain doors that only specific people can open, or, you know, certain tools that only trained staff can use. It's all about control and safety, which, you know, makes sense.
The message itself, "your IT administrator has limited," is quite direct, telling you exactly who is responsible for the restriction. It's a clear statement that, you know, the boundaries are in place because of a decision made by the team looking after the digital environment. This is, you know, usually for the greater good of the organization, even if it feels a bit inconvenient at the moment.
The Personal Connection of "Your"
The word "your" in "your IT administrator has limited" is, you know, quite important here. It points to something belonging to you, or something that is connected with you, like your specific user account, your workstation, or, you know, your access privileges. As a matter of fact, "your" is the possessive form of the pronoun "you," and it really shows ownership or a strong association. So, when the system says "your IT administrator," it means the person or team responsible for the technology you use, the tools that, you know, belong to your work setup.
This word "your" makes the message personal because it directly refers to the impact on what you, as an individual user, can do. It's not just a general system message; it's about what you are experiencing with your tools. You know, it's about how something belongs to or is associated with the person being addressed, which, you know, in this case, is you. So, the restriction is directly affecting your ability to operate, which, you know, is why it feels so personal.
Using "your" here helps to clarify that the limitation is on something you possess or are directly interacting with, like your computer files, your ability to install software on your machine, or, you know, your access to certain parts of the network. It's a way of saying, "this is about what you can do with your assigned resources," which, you know, makes the message very clear and relevant to your immediate situation.
Common Reasons for IT Limitations
IT administrators don't just put limits in place, you know, for fun or to make things difficult. There are usually very good, practical reasons behind these decisions, which are, you know, often about keeping the entire system healthy and safe. It's a bit like, you know, a city having traffic laws to keep everyone moving and prevent accidents. These rules are, you know, pretty much always there to serve a bigger purpose.
Many of these reasons stem from the need to protect valuable company information and ensure that all digital tools work as they should. It's, you know, a balancing act between giving people the freedom to do their work and, you know, making sure that freedom doesn't accidentally cause problems for everyone else. So, there's a lot of thought that goes into these choices, which, you know, is understandable.
Understanding these underlying reasons can, you know, help make those "limited" messages a bit less frustrating. When you know why something is happening, it's, you know, usually easier to accept or, at least, to talk about it with your IT team. So, let's look at some of the main drivers behind these common IT restrictions, which, you know, are pretty standard across many organizations.
Security and Data Protection
One of the biggest reasons for IT limitations is, you know, keeping things secure. In today's digital world, there are, you know, all sorts of threats, from viruses to hackers, that can try to get into a company's systems. If someone, say, accidentally downloads something harmful or visits a risky website, it could, you know, put everyone's data at risk. So, restrictions are a way to build a protective wall, which, you know, is really important.
IT administrators use these limits to stop unauthorized access to sensitive information. For example, they might prevent you from installing software that hasn't been checked for security flaws, or, you know, block access to websites known to spread malicious content. This is, you know, basically about preventing problems before they even start, which, you know, saves a lot of trouble later.
Think of it like, you know, having a security guard at the entrance of a building. The guard isn't there to annoy you, but to make sure only authorized people and safe items enter. Similarly, IT restrictions are there to protect the company's digital assets, which, you know, include everything from customer lists to important financial records. It's a pretty big job, actually.
Compliance and Regulatory Requirements
Many industries have strict rules and laws about how they handle data, especially personal or financial information. These are, you know, called compliance or regulatory requirements. For example, healthcare organizations have rules like HIPAA, and financial institutions have their own sets of regulations. If a company doesn't follow these rules, it could face huge fines or, you know, lose trust. So, IT limitations often help meet these standards, which, you know, is a legal necessity.
IT administrators set up systems to make sure the company stays within these legal boundaries. This might mean, for example, that certain types of data can only be accessed by specific people, or, you know, that files can't be saved to personal cloud storage services. These restrictions are, you know, not just company policy but often legal obligations. It's, you know, about keeping the company on the right side of the law.
The "your IT administrator has limited" message, in this context, might mean that your attempt to do something goes against one of these important rules. It's a reminder that, you know, there are external standards that the company must follow, and the IT team is helping to make sure that happens. So, it's, you know, a very serious aspect of their work.
System Stability and Performance
Another important reason for limitations is, you know, keeping all the computer systems running smoothly and quickly. When people install unapproved software, change system settings, or, you know, download large files constantly, it can sometimes slow down the entire network or cause computers to crash. This, you know, affects everyone's ability to get their work done. So, IT puts limits in place to prevent these kinds of disruptions, which, you know, is pretty sensible.
Imagine if everyone in an office could, you know, just plug in any device or install any program they found online. Some of those things might, you know, conflict with existing software, use up too much computer power, or even, you know, introduce bugs. These issues can lead to system downtime, which, you know, costs the company time and money. So, the restrictions are about maintaining a reliable work environment, which, you know, is something everyone benefits from.
IT administrators aim to create a stable and predictable computing environment. By controlling what can be installed or changed, they can, you know, reduce the chances of things going wrong. This means fewer tech support calls, less downtime, and, you know, generally a more efficient workplace. It's, you know, all about keeping the digital machinery well-oiled and running.
Resource Management and Cost Control
Companies have budgets for their technology, and, you know, every piece of software, every network connection, and every bit of storage costs money. IT limitations can, you know, help manage these resources effectively and keep costs down. For example, if everyone could just download paid software without approval, the company's expenses could, you know, quickly get out of hand. So, restrictions help make sure resources are used wisely, which, you know, is a smart business move.
IT administrators might limit access to certain high-bandwidth websites or, you know, prevent the use of personal cloud storage services to avoid unexpected data transfer costs. They might also, you know, standardize software to get better bulk pricing and reduce the complexity of managing many different applications. It's, you know, about getting the most value out of the company's tech investments.
When "your IT administrator has limited" something, it could be part of a broader strategy to manage the company's digital resources. This ensures that essential services are always available and that money is spent on the tools that, you know, truly benefit the organization. So, it's, you know, a very practical aspect of their role.
Software Licensing and Standardization
Software often comes with licenses that dictate how many people can use it or on how many devices it can be installed. If a company uses software without the proper licenses, it can face legal problems and fines. So, IT administrators put limits on what software can be installed to ensure, you know, that everything is properly licensed. This is, you know, a legal and financial safeguard.
Standardizing software means that everyone uses the same versions of programs, which, you know, makes it much easier for the IT team to support. If everyone has different versions of, say, a word processor, it becomes, you know, very hard to troubleshoot problems or ensure compatibility. So, by limiting what can be installed, IT helps keep things consistent, which, you know, simplifies support.
These limitations help the IT department manage software updates, security patches, and overall system compatibility more effectively. It means that when a new update comes out, they can roll it out to everyone at once, knowing it will work. So, "your IT administrator has limited" in this case is, you know, about making the whole software ecosystem manageable and legal.
Types of Restrictions You Might Encounter
The message "your IT administrator has limited" can appear in many different situations, depending on what you're trying to do. These limitations are, you know, usually very specific to certain actions or areas of your computer. It's, you know, a bit like having different keys for different locks; each restriction addresses a particular potential issue. So, let's look at some common examples, which, you know, you might have already seen.
Knowing the different types of restrictions can, you know, help you understand why a particular message popped up. It also gives you a better idea of what to expect in a managed work environment. These are, you know, pretty standard ways that IT teams keep things secure and running well, which, you know, is their main goal.
Each type of limitation serves one or more of the reasons we just talked about, like security or system stability. They are, you know, carefully chosen to protect the organization without, you know, overly hindering productivity. So, here are some of the most frequent types of restrictions you might come across, which, you know, are very common.
Software Installation and Updates
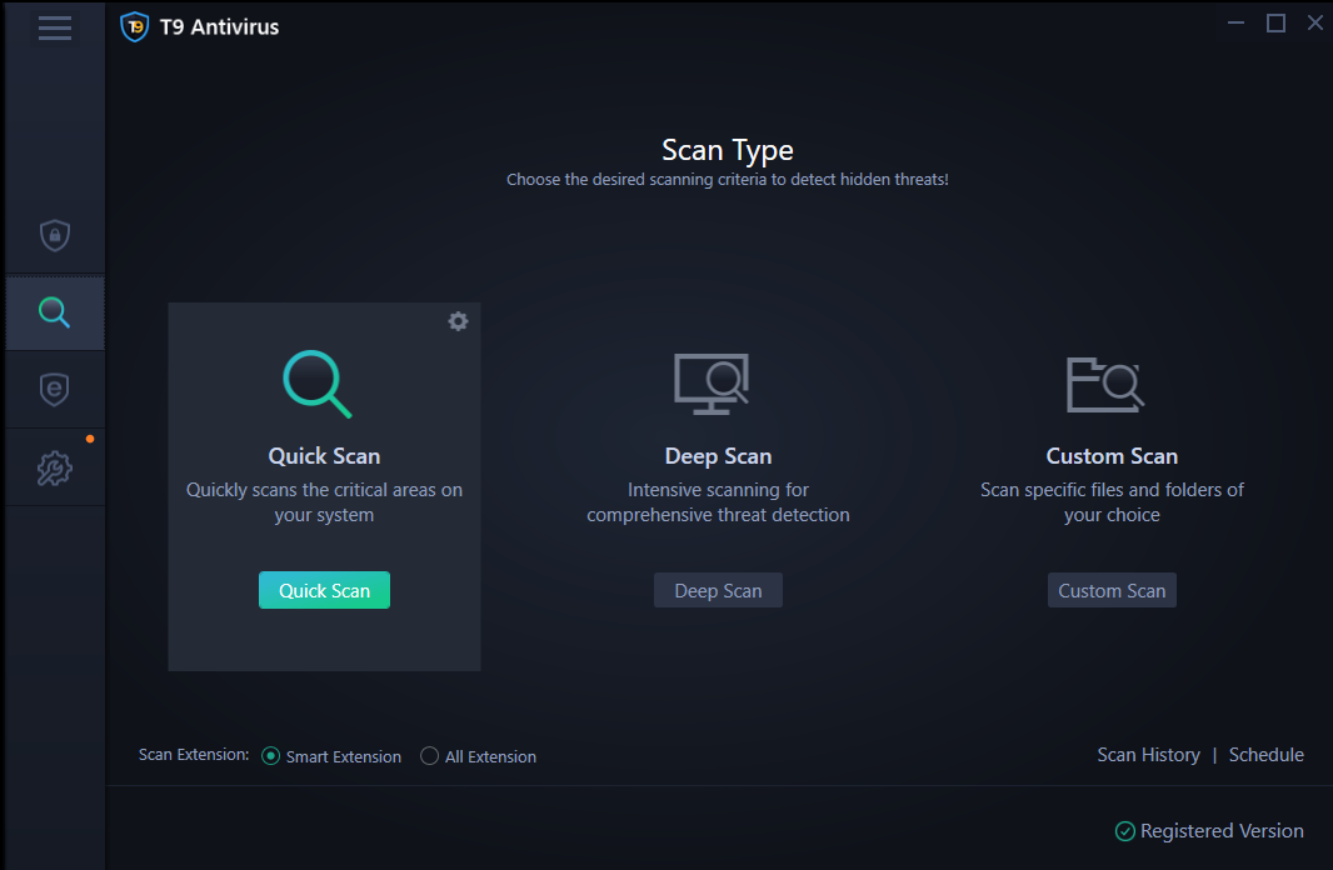
This is, you know, probably one of the most common restrictions. When you try to install a new program, or sometimes even update an existing one, you might see the message. This means that, you know, you don't have the necessary administrative rights to make changes to the system's software. It's a primary way to control what runs on company computers, which, you know, is important for security.
The IT team usually wants to approve all software to make sure it's safe, compatible with other systems, and, you know, properly licensed. Unapproved software could introduce viruses, create conflicts, or, you know, violate licensing agreements. So, "your IT administrator has limited" your ability to install software is, you know, a very strong protective measure.
If you need a new program for your work, the proper way to get it is, you know, usually to submit a request to your IT department. They can then, you know, review it, ensure it meets all the requirements, and install it for you. This process, you know, keeps everything orderly and secure.
Website and Application Access
Sometimes, you might find that certain websites or online applications are blocked. When you try to reach them, you get the message. This restriction is often about preventing access to sites that are, you know, known to be risky, contain inappropriate content, or, you know, are simply not related to work. It's a way of keeping the network safe and, you know, people focused.
IT administrators might block categories of websites, like social media, streaming services, or, you know, gambling sites, during work hours to reduce distractions and conserve network bandwidth. They also, you know, block known phishing sites or sites that host malware to protect the company's systems from cyber threats. This is, you know, a very direct security measure.
If a website or application that you need for your job is blocked, you'll, you know, usually need to contact your IT department. They can then, you know, review your request and potentially unblock it if it's, you know, genuinely necessary for your work. So, communication is key here, which, you know, is pretty much always the case.
USB and External Device Usage
Plugging in USB drives, external hard drives, or other devices can, you know, sometimes trigger a "your IT administrator has limited" message. This is a common security measure to prevent the spread of malware and to control data leakage. A USB stick, for example, could, you know, easily carry a virus from a home computer into the company network, or, you know, be used to copy sensitive information out of the office. So, these limits are there for a reason, which, you know, is very serious.
Many organizations have policies that restrict or completely block the use of personal external storage devices. This helps protect against both incoming threats and, you know, outgoing data breaches. Some companies might allow specific, company-issued USB drives that are, you know, encrypted and regularly scanned for viruses. It's all about managing risk, which, you know, is a big part of IT's job.
If you need to use an external device for work, you should, you know, definitely check with your IT team first. They can advise you on the proper procedures or, you know, provide you with an approved device. This ensures that, you know, you're not accidentally creating a security risk.
Network and File Share Permissions
Access to specific network drives, folders, or shared files is often controlled by IT administrators. If you try to open a folder or save a file to a location where you don't have permission, you'll, you know, likely see the limitation message. This is about ensuring that only authorized individuals can access or modify certain data, which, you know, is crucial for data integrity and confidentiality.
These permissions are set up based on your role and your need to access certain information. For example, the finance department might have access to financial records that, you know, other departments do not. This helps maintain a clear structure for data access and prevents unauthorized viewing or, you know, accidental changes to important documents. It's, you know, a very fundamental part of data security.
If you believe you need access to a particular network resource for your job, you should, you know, talk to your manager or IT department. They can then, you know, review your request and adjust your permissions if it's, you know, appropriate for your role. This ensures that, you know, everyone has what they need without giving away too much.
System Settings and Configuration
Attempting to change core system settings, like network configurations, security settings, or, you know, installing printer drivers, can also lead to the "your IT administrator has limited" message. These settings are often locked down to maintain system stability, ensure security policies are enforced, and, you know, prevent users from accidentally breaking something. It's about keeping the core operating system sound, which, you know, is pretty important.
Allowing users to freely change these settings could, you know, lead to a wide range of problems, from network connectivity issues to security vulnerabilities. IT administrators configure these settings in a way that, you know, best serves the organization's needs and security posture. So, these restrictions are a way to maintain a consistent and secure operating environment, which, you know, is really important for everyone.
If you need a system setting changed or a new piece of hardware configured, you should, you know, always reach out to your IT support. They have the necessary permissions and expertise to make these changes safely and correctly, which, you know, prevents potential issues. Learn more about on our site.
How to Approach IT Limitations
Encountering "your IT administrator has limited" can be a bit annoying, but, you know, there are good ways to handle it. It's not about trying to get around the restrictions, but rather about understanding them and, you know, working within the established framework. A good approach can often lead to a quicker resolution and, you know, a better understanding between you and your IT team. So, let's look at some helpful steps, which, you know, are usually pretty effective.
Remember, IT teams are there to help, but they also have a big responsibility to protect the company's digital assets. Approaching them with a clear explanation of your needs and an understanding of their role can, you know, really make a difference. It's about collaboration, which, you know, is always a good thing.
By following these steps, you can, you know, usually find a solution that works for everyone, ensuring you can do your job effectively while also respecting the company's security and operational policies. So, these tips are, you know, pretty much always a good idea to keep in mind.
Understanding the Policy
Before you do anything else, it's a good idea to, you know, try and understand why the limitation is in place. Many companies have written IT policies or acceptable use policies that, you know, explain these kinds of restrictions. Taking a moment to look at these documents, if they are available, can often, you know, answer your questions. This is, you know, a very good first step.
Knowing the policy can help you figure out if your request aligns with company rules or if there's a specific reason why something is blocked. It also shows your IT team that, you know, you've done your homework, which, you know, can make your conversation with them more productive. So, a little bit of research can, you know, go a long way.
If you can't find the policy documents, or if they're not clear, that's perfectly fine. The main point is to, you know, have some idea of the context before you reach out. This helps frame your request in a way that, you know, makes sense to the IT department.
Communicating with Your IT Team
If you encounter a restriction that genuinely prevents you from doing your work, the best thing to do is, you know, to contact your IT support team. When you do, be clear and specific about what you were trying to do, what message you received, and, you know, why you need that particular access or software. This helps them understand your situation, which, you know, is really important.
Explain the business need behind your request. For example, instead of just saying "I need to install this program," say "I need to install [Program Name] because it's, you know, essential for [specific task] and helps me [achieve a business goal]." This gives them the context they need to, you know, evaluate your request properly.
Be patient and polite. IT teams are often busy, and, you know, they have to consider the impact of every change on the entire system. They might need time to review your request, especially if it involves, you know, a new piece of software or a change to security settings. A good attitude can, you know, really help in getting a positive outcome.
Finding Alternative Solutions
Sometimes, the IT team might not be able to grant your specific request due to security, compliance, or, you know, other reasons. In such cases, it's helpful to be open to alternative solutions. Your IT administrator might, you know, suggest a different, approved tool that can achieve the same goal, or, you know, a different way to access the information you need. This is, you know, a very practical approach.
For instance, if you can't install a specific file transfer program, they might, you know, point you to an approved cloud storage service or a secure file-sharing method that the company already uses. Being flexible and willing to explore these alternatives can, you know, often lead to a solution that works for everyone. It's about achieving the outcome, not just, you know, one specific method.
Working with your IT team to find these solutions shows that, you know, you understand the need for security and policy, and that you're willing to cooperate. This collaborative spirit can, you know, really strengthen the working relationship. So, always be ready to discuss other options, which, you know, can be very helpful.
Frequently Asked Questions About IT Restrictions
Why does my IT administrator limit what I can do?
Your IT administrator limits what you can do for several very important reasons, actually. These usually include protecting the company's data from cyber threats, making sure the company follows legal and industry regulations, and, you know, keeping all the computer systems running smoothly and reliably. It's also about managing software licenses and, you know, making sure resources are used wisely. So, it's for the overall good of the organization, which, you know, is pretty much always the case.
What kind of things can an IT administrator restrict?
An IT administrator can restrict, you know, quite a few things. This often includes preventing you from installing new software or updates, blocking access to certain websites or online applications, and, you know, limiting the use of USB drives or other external devices. They can also control your access to specific network folders and files, and, you
Fix - Your IT Administrator Has Limited Access (Page Not Available)

Your IT administrator has limited access : WindowsHelp

Your IT administrator has limited access to some areas of this app