How To Add Security Group To EC2 Instance For Better Cloud Safety
Keeping your cloud servers safe is a big deal, really. When you put your applications and data on the internet, you want to make sure only the right people and services can get to them. This is where a security group for your EC2 instance comes into play. It's like having a digital bouncer for your server, deciding who gets in and who stays out. Getting this part right means your applications stay protected from unwanted visitors, which is pretty important, you know?
A lot of folks starting out with cloud computing sometimes miss how important these security settings are. They might set up a server, get their website working, but then forget to lock down the digital doors. This can lead to big problems, like someone getting access to your private information or even taking over your server. So, learning how to add security group to EC2 instance is not just a technical step; it's a fundamental part of keeping your online presence secure. It’s a bit like making sure your front door has a good lock before you leave the house, actually.
This guide will walk you through the whole process, showing you how to set up these important protections. We'll look at why they matter, how they work, and the steps you need to take to make sure your EC2 instances are properly guarded. You'll see how to manage incoming connections and outgoing connections, making sure your server can talk to the services it needs to, and nothing else. It's a key piece of the puzzle for anyone running things in the cloud, so you can feel more confident about your online systems, you know?
Table of Contents
- What Are Security Groups? Your EC2 Instance's First Line of Defense
- Why Security Groups Matter for Your EC2 Instances
- How to Add Security Group to EC2 Instance (When Launching a New One)
- How to Add Security Group to EC2 Instance (For a Running Instance)
- Common Use Cases for Security Groups
- Best Practices for Managing EC2 Security Groups
- Troubleshooting Common Security Group Issues
- Frequently Asked Questions About EC2 Security Groups
What Are Security Groups? Your EC2 Instance's First Line of Defense
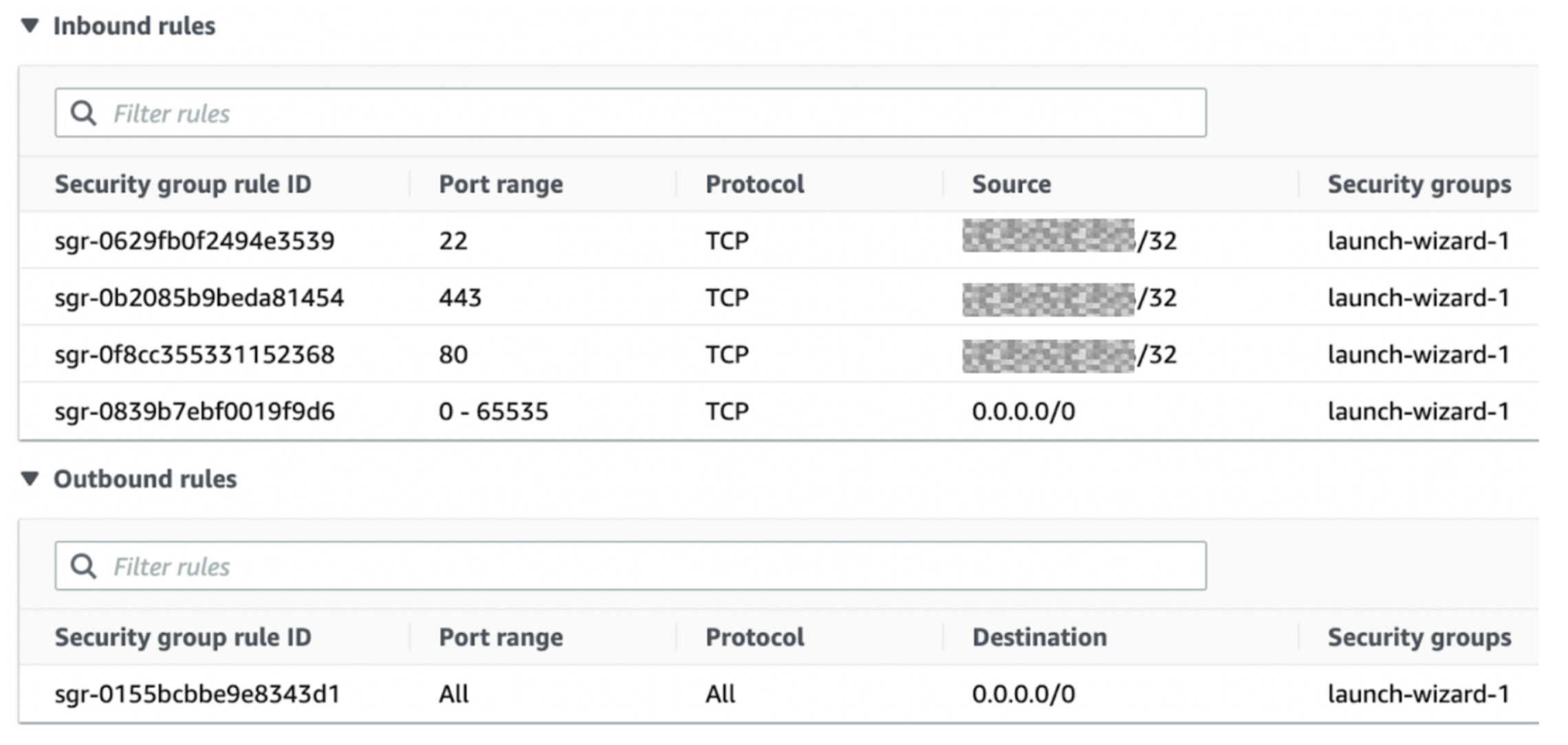
A security group is, in a way, like a virtual firewall that controls traffic for one or more EC2 instances. When you add security group to EC2 instance, you are setting up rules that say what kind of network traffic is allowed to come in (inbound) and go out (outbound) from your instance. It’s a very basic yet powerful security feature, actually. Every EC2 instance has to have at least one security group, and you can give an instance several, too.
These rules are pretty important. For example, you might want to allow web traffic on port 80 or 443 to reach your web server, but block everything else. Or maybe you only want specific computers, like your office network, to be able to connect to your server using SSH. Security groups let you set up these very precise permissions, which is quite helpful, you know?
The Stateful Nature of Security Groups
One neat thing about security groups is that they are "stateful." What this means is that if you allow traffic to come into your instance, the responses for that traffic are automatically allowed to go back out. You don't need to create a separate outbound rule for the reply. For example, if you let someone connect to your web server on port 80, the server's answers back to that person will automatically be allowed to leave. This makes managing them a bit simpler, apparently.
Why Security Groups Matter for Your EC2 Instances
The internet can be a pretty wild place, so your servers need protection. Security groups are your first line of defense against unwanted access. Without proper security group rules, your EC2 instance could be open to anyone on the internet. This could lead to all sorts of problems, like unauthorized data access, server attacks, or even your instance being used for bad things. So, you really want to add security group to EC2 instance with care, you know?
Think about it like this: if you have a shop, you wouldn't just leave the doors wide open all the time. You'd have locks, maybe an alarm, and you'd only let customers in during business hours. Security groups do a similar job for your digital assets. They help you control who gets to "walk through the door" of your server, which is actually very important for overall safety.
How to Add Security Group to EC2 Instance (When Launching a New One)
When you're launching a brand new EC2 instance, you get the chance to pick or create a security group right away. This is usually the easiest way to get things set up from the start. You'll be asked about it during the instance launch wizard, so it's hard to miss, you know?
Step-by-Step: Launching with a New Security Group
Let's walk through how you would add security group to EC2 instance when you're making a new one:
- Go to the EC2 Dashboard: First, log into your AWS Management Console and find the EC2 service.
- Start Launching an Instance: Click on "Launch Instance" to begin the process. You'll go through several steps like choosing an Amazon Machine Image (AMI) and instance type.
- Configure Instance Details: After picking your AMI and instance type, you'll move to configuring instance details. Here, you'll set things like the number of instances, network, and subnet.
- Add Storage: Next, you'll add storage volumes for your instance.
- Add Tags: You can add tags to help organize your resources. This is pretty useful for keeping track of things.
- Configure Security Group: This is where the magic happens. On the "Configure Security Group" page, you have two main choices:
- Create a new security group: This is what you'll usually do if you need specific rules that don't exist yet. You'll give it a name and a description. Then, you'll add rules. For example, to allow web traffic, you'd add a rule for "HTTP" on port 80, and maybe "HTTPS" on port 443. For "Source," you can pick "Anywhere" (0.0.0.0/0) for public access, or a specific IP address range if you want to limit access. You could also add a rule for SSH access on port 22, typically from "My IP" or a specific range.
- Select an existing security group: If you've already made a security group with the rules you need, you can just pick it from the list. This saves time, especially if you have common setups.
- Review and Launch: After setting up your security group, you'll review all your settings. Make sure everything looks right, and then click "Launch." You'll also pick an existing key pair or create a new one to connect to your instance.
And that's it! Your new EC2 instance will launch with the security group rules you set up. It's a pretty straightforward process, so you can feel good about it.
Using an Existing Security Group for a New Instance
Sometimes, you already have a security group that does just what you need. Maybe you have one for all your web servers, allowing HTTP and HTTPS traffic. When launching a new instance that will also be a web server, you can just pick that existing security group. This helps keep things consistent and saves you from making the same rules over and over. It's a smart way to work, you know?
How to Add Security Group to EC2 Instance (For a Running Instance)
What if your EC2 instance is already up and running, and you need to change its security rules? Maybe you forgot to open a port, or you want to add another layer of protection. You can definitely add security group to EC2 instance even after it's been launched. This is a common task for administrators, and it's pretty simple to do.
Changing Security Groups via the AWS Management Console
Here's how you adjust security groups for an instance that's already active, using the console:
- Go to the EC2 Dashboard: Open the AWS Management Console and head to the EC2 service.
- Select Your Instance: In the left navigation pane, click on "Instances." Find the specific EC2 instance you want to change and select it.
- Modify Security Groups: With your instance selected, look at the "Actions" button at the top. Click it, then go to "Security," and then "Change security groups."
- Add or Remove: A window will pop up showing the security groups currently linked to your instance. You can add more security groups by checking the boxes next to their names. If you want to take one away, just uncheck its box. Remember, you can have several security groups on one instance, which is quite flexible.
- Apply Changes: Once you've made your choices, click "Save." The changes will take effect pretty quickly, which is handy.
This method is good for quick adjustments and for seeing all your options visually. It's a pretty common way to manage things, actually.
Updating Security Groups with AWS CLI
For those who like working with command lines or need to automate tasks, the AWS Command Line Interface (CLI) is a great tool. You can use it to add security group to EC2 instance, or to swap them out. This is very useful for scripting or managing many instances at once.
The command you'll typically use is `modify-instance-attribute`. Here's a basic example:
aws ec2 modify-instance-attribute --instance-id i-0abcdef1234567890 --groups sg-0123456789abcdef0 sg-0fedcba9876543210In this command:
- `--instance-id`: This is the unique identifier for your EC2 instance.
- `--groups`: This is where you list the IDs of all the security groups you want the instance to be associated with. If you want to keep existing ones, you must include them in this list. If you leave one out, it will be removed.
Using the CLI gives you a lot of control and is great for repeatable actions. It's a bit more technical, but very powerful, you know?
Common Use Cases for Security Groups
Understanding how to add security group to EC2 instance is one thing, but knowing what rules to set is another. Here are some common scenarios where security groups are absolutely key:
Web Server Access (HTTP/HTTPS)
If your EC2 instance is hosting a website, you need to let people visit it. This means allowing incoming traffic on specific ports:
- HTTP (Port 80): For unencrypted web traffic.
- HTTPS (Port 443): For secure, encrypted web traffic.
You'll usually set the source for these rules to "Anywhere" (0.0.0.0/0) so anyone on the internet can reach your site. This is a pretty standard setup, you know?
SSH for Remote Access
To connect to your Linux EC2 instance and run commands, you'll use SSH (Secure Shell). This typically uses port 22. It's very important to be careful with this rule. Instead of opening it to "Anywhere," you should try to limit the source to your specific IP address or a range of IP addresses that you trust. This really helps keep your server safe, actually.
Database Connections
If you have a database server on an EC2 instance, you definitely don't want it open to the whole world. You'll typically set rules that only allow connections from other EC2 instances in your application tier, or perhaps from specific development machines. For example, MySQL uses port 3306, PostgreSQL uses 5432, and SQL Server uses 1433. You would set the source to the security group ID of your application servers, which is a very good security practice.
Internal Application Communication
Sometimes, different parts of your application run on different EC2 instances. For them to talk to each other, you'll need security group rules that allow this internal communication. You can do this by setting the source of an inbound rule to another security group ID. This means only instances associated with that specific security group can connect, which is quite clever.
Best Practices for Managing EC2 Security Groups
Just knowing how to add security group to EC2 instance isn't enough. You also need to follow some good habits to keep your cloud environment secure. These practices help prevent common mistakes and make your setup more resilient.
The Least Privilege Rule
This is a fundamental security idea. It means you should only grant the absolute minimum permissions needed for something to work. For security groups, this means:
- Only open ports that are truly necessary. If your server doesn't need port 21 (FTP), don't open it.
- Limit source IP addresses as much as possible. Instead of 0.0.0.0/0, use your office IP, a VPN IP, or another security group ID.
Following this rule makes it much harder for attackers to find an open door, which is pretty smart, you know?
Using Specific IP Ranges
Whenever you can, avoid using 0.0.0.0/0 for inbound rules, especially for sensitive ports like SSH (22) or RDP (3389). Instead, find out your public IP address and use that, or a specific range for your company network. This significantly reduces the exposure of your instance to the broader internet, which is a very good thing.
Clear Naming Conventions
When you create security groups, give them names and descriptions that make sense. Something like "web-server-sg" or "database-access-from-app" is much better than "sg-123." Clear names help you and your team quickly understand what each security group does, which is pretty helpful, you know?
Regular Reviews and Cleanups
Over time, your needs might change. You might shut down an old application, or a team member might leave. It's a good idea to regularly check your security groups. Remove any rules that are no longer needed, and delete security groups that aren't attached to any instances. This helps keep your environment tidy and reduces potential security risks. It's like cleaning out your closet, you know? Get rid of what you don't use anymore.
Troubleshooting Common Security Group Issues
Sometimes, even after you add security group to EC2 instance, things don't quite work as expected. Here are a few common problems and how to think about them:
- "I can't SSH into my instance!":
- Check if port 22 is open in the security group.
- Make sure the source IP address in the rule includes your current public IP.
- Verify you're using the correct key pair.
- "My website isn't loading!":
- Is port 80 (HTTP) and/or 443 (HTTPS) open in the security group?
- Is the source for these rules set to 0.0.0.0/0 (Anywhere)?
- Is your web server software actually running on the instance?
- "My application can't connect to the database!":
- Check the database port (e.g., 3306 for MySQL) in the database server's security group.
- Make sure the source for that rule is the security group ID of your application server.
- Also, check the outbound rules on the application server's security group to ensure it can reach the database.
Remember, security groups are stateless for *outbound* traffic if the *inbound* connection wasn't initiated by your instance. But for traffic initiated *by* your instance, the replies are allowed. It's a subtle point, but important. Always check both inbound and outbound rules if you're having trouble with connections.
Frequently Asked Questions About EC2 Security Groups
People often have similar questions about how these virtual firewalls work. Here are some common ones, you know?
Can I add multiple security groups to an EC2 instance?
Yes, absolutely! You can attach several security groups to a single EC2 instance. When you do this, the rules from all attached security groups are effectively combined. If any one of the attached security groups allows a certain type of traffic, that traffic will be permitted. This can be very useful for organizing rules, like having one security group for SSH access and another for web traffic, which is pretty handy.
What is the difference between a security group and a network ACL?
This is a common question, actually. Both security groups and network ACLs (Access Control Lists) help with network security, but they work at different levels. Security groups operate at the instance level, meaning they control traffic to and from your specific EC2 instances. They are stateful, as we talked about, so if traffic is allowed in, the response is allowed out automatically. Network ACLs, on the other hand, operate at the subnet level. They are stateless, meaning you have to create separate rules for both inbound and outbound traffic. They act as a firewall for an entire subnet. Most people usually start with security groups because they are simpler for instance-level control, but network ACLs can add another layer of network security, you know?
How do I allow SSH access to my EC2 instance?
To allow SSH access, you need to add an inbound rule to your EC2 instance's security group. The rule should specify "SSH" as the type (which means port 22), and you should set the source to the IP address or range from which you will connect. For instance, you could use "My IP" if you're connecting from your current location, or a specific CIDR block like "203.0.113.0/24" if you have a fixed office network. It's very important to avoid setting the source to "Anywhere" (0.0.0.0/0) for SSH, unless you have a very specific and temporary need, as this opens your server to the entire internet for SSH attempts, which is not good for safety.
Getting your security groups right is a huge part of keeping your cloud setup safe and sound. By taking the time to understand how to add security group to EC2 instance, and by following good security practices, you can protect your applications and data from a lot of common online threats. Remember, security is an ongoing effort, not a one-time thing. So, keep learning, keep checking your rules, and keep your systems secure. You can learn more about cloud security fundamentals on our site, and link to this page for more EC2 basics.

Group Project 1: Create EC2 instance And configure security group
Add Security Group To Calendar Permissions - Vitia Rosamond

From creating key,volume,security group to launching EC2 instance from