Port Scan Explained: How To Check Your Network's Open Doors For Better Security
Have you ever thought about the digital doors to your home or business network? Just like a physical building has entrances and exits, your internet connection has thousands of "ports" that allow different kinds of information to flow in and out. Knowing which of these ports are open, and what's using them, is a very big part of keeping your network safe. A port scan is that essential check, helping you see exactly what's visible to the outside world, so you can make smart choices about your online defenses.
Every time you browse a website, send an email, or even play an online game, you are, in a way, using these digital doors. Services like web servers, mail servers, and game servers each have their own specific port numbers they listen on. If these ports are left open without proper security, they could, you know, potentially become a way for unwanted visitors to peek into your network or even cause trouble. It's a bit like leaving a window open in your house; you want to be sure only good things come through.
Understanding what a port scan is, and how it helps you manage your network's visibility, is really important for anyone connected to the internet today. Whether you are a small business owner, a home user trying to set up a new service, or just someone curious about network safety, knowing about these digital doorways can, quite literally, give you peace of mind. So, let's talk more about how these scans work and what they can show you, actually.
Table of Contents
- What Exactly Is a Port Scan?
- Why Port Scans Are Important for Your Network's Safety
- How Port Scanning Works: The Basics
- Using a Port Checker Tool for Easy Scans
- Interpreting Your Scan Results: Open, Closed, or Filtered?
- Securing Your Network After a Scan: What to Do Next
- Common Questions About Port Scans
- Taking Control of Your Network's Safety
What Exactly Is a Port Scan?
A port scan, you see, is simply a method of checking which ports on a network device, like a computer or a server, are open and listening for connections. Think of it as knocking on every single door of a building to see which ones are unlocked or have someone ready to answer. Each port number, from 0 to 65535, is a specific channel for different types of network communication. For example, web traffic usually goes through port 80 or 443, while email might use port 25 or 587. It's all very specific, you know.
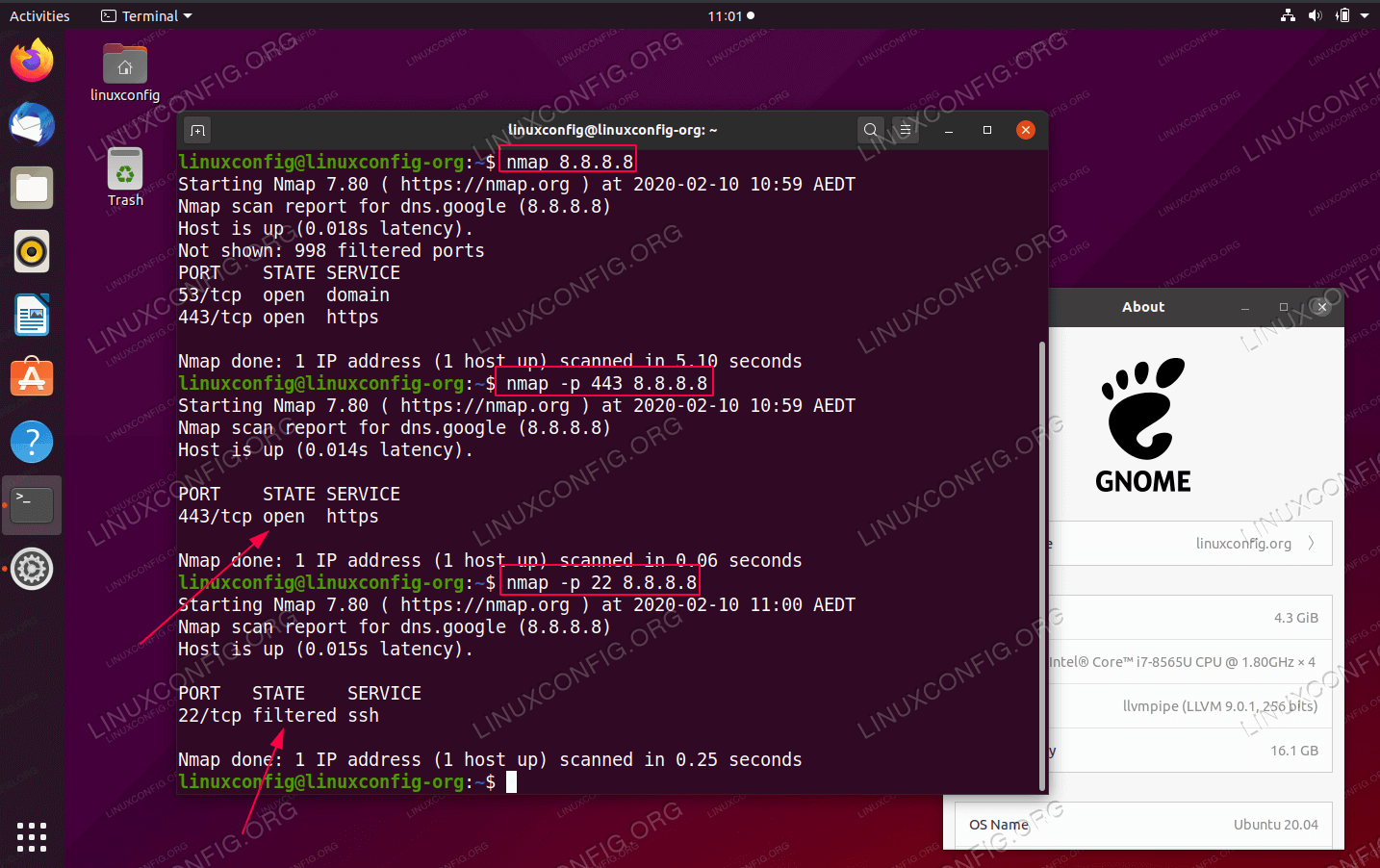
When you perform a port scan, a tool sends out connection requests to a range of these ports on a target IP address. The way the target responds tells you the status of that particular port. A response might indicate the port is open, meaning a service is actively listening there. Or, it might be closed, meaning no service is running on that port. Sometimes, a port might appear "filtered," which means a firewall is blocking the connection and hiding its true status. This information is, in fact, incredibly useful.
This process, while it sounds technical, is actually quite straightforward for the tools that do it. They systematically go through the ports, gather the responses, and then present them in an easy-to-understand way. It's how you get a clear picture of your network's external footprint, and, you know, what services might be visible to anyone looking in from the internet. This kind of check is a foundational step in network safety, really.
Why Port Scans Are Important for Your Network's Safety
The main reason to do a port scan is for network security, actually. An open port isn't bad on its own, but if there's no good reason for it to be open, or if the service running on it isn't properly secured, it can become a potential weakness. Bad actors on the internet are constantly scanning for open ports to find vulnerable services they can exploit. They might be looking for old, unpatched software, or misconfigured services that allow unauthorized access. So, knowing your open ports is like knowing where your network's weak spots might be, you see.
Beyond security, port scans are also very helpful for troubleshooting. If you're trying to set up a new server, like a game server or a home media server, and you can't access it from outside your network, a port scan can tell you if the necessary ports are actually open. It helps you check if your port forwarding rules are working correctly on your router or firewall. This saves a lot of time and frustration, more or less, when trying to get things running.
For businesses, mapping a company's network perimeter is a very crucial use for port scans. It helps IT teams understand what services are reachable from the internet, check firewall rules, and confirm that only intended services are exposed. This proactive approach helps maintain a strong security posture and reduces the chances of unexpected access. It's a basic, yet powerful, way to manage your network's outer shell, as a matter of fact.
How Port Scanning Works: The Basics
At its heart, a port scan works by sending out specially crafted network packets to a target's IP address and then observing the responses. There are two primary types of network communication protocols that port scans typically check: TCP (Transmission Control Protocol) and UDP (User Datagram Protocol). Each has its own way of responding, and a good port scanner will, you know, use both to get a complete picture. This combination ensures very accurate results.
TCP scanning, for instance, involves attempting to establish a "handshake" with a port. When you try to connect to a web server, your computer and the server go through a three-step process to confirm they are ready to talk. A port scanner sends the first step of this handshake. If the target responds with the second step, the scanner knows the port is open and listening. If it sends a "reset" signal, the port is likely closed. If there's no response, or a specific error, a firewall might be blocking it. This method is, quite honestly, very reliable.
UDP scanning is a little different and, frankly, a bit trickier. UDP is a connectionless protocol, meaning it doesn't do a handshake. A UDP scan sends a small packet to a port and waits for an "ICMP Port Unreachable" message. If it gets that message, the port is closed. If it gets no response, or an application-specific response, the port is likely open. Because many UDP services don't respond at all, it can be harder to tell the difference between an open port and a filtered one. However, combining both TCP and UDP techniques gives you, you know, a very comprehensive view.
Many advanced port scanners, including the ones mentioned in "My text," are based on powerful tools like Nmap. Nmap is a well-known, free, and open-source network scanner that has been used by security professionals for years. Using an online tool based on Nmap means you get the benefit of its accuracy and capabilities without needing to install complex software yourself. It's a pretty convenient way to get professional-grade results, in a way.
Using a Port Checker Tool for Easy Scans
You don't need to be a network expert to run a port scan. Thanks to online port checker tools, it's actually quite simple. Our port checker, for instance, is designed to be very user-friendly. You simply enter the domain name or IP address you want to check, and then, you know, you can specify the port number or a range of ports you are interested in. It's a very quick process, often taking less than five minutes for common checks.
These tools combine traditional TCP and UDP scanning techniques to ensure highly accurate results. They can map a company’s network perimeter, check firewall rules, and determine if its services are reachable from the internet in a single scan. This kind of comprehensive check helps you find open ports, check for vulnerabilities, and identify services running on any server or IP address. It's a fast and very reliable way to get critical information, honestly.
Our open port scanner online lets you check your external IP address and detect open ports on your connection. This is incredibly useful for finding out if your port forwarding is set up correctly, for example, if you're trying to host a game server or access a home camera system from outside. It will also help you determine if those open ports need to be closed to provide more network security and fewer vulnerabilities. It's all about making sure your network is buttoned up, you know.
With an online TCP port scanner, you can scan an IP address for open ports and even see what services, like Apache web servers, mail servers, SSH, FTP, MySQL, Telnet, or DNS, are running on them. You can check your IP for open ports and vulnerabilities in under five minutes. Just enter your domain or IP address and scan 29 of the most common and vulnerable ports instantly. This helps you protect your network and secure your infrastructure, very quickly.
The port.tools, for instance, works well on both desktop and mobile devices, making it accessible wherever you are. Its powerful yet intuitive user interface makes scanning any port much easier. To perform a quick port test, you just access the tool, add the port number you are testing, and hit scan. It's really that simple, you know.
Besides the port scanner, we also offer a set of other tools to enhance your productivity, such as a MAC vendor lookup, MAC address generator, and AS number lookup. Our DNS checker, for example, provides name server propagation checks instantly, which is very useful if you have changed nameservers and need to confirm they are updated across the internet. These networking tools, including the ports scanner tool, ASN whois lookup, and more, are designed to help you manage your network details effectively. You can even check server headers by simply entering a URL, or ping any IPv6 address by sending ICMP packets to a given host. We also have an IP subnet calculator for both IPv4 and IPv6 subnet calculations. It's a pretty complete set of utilities, as a matter of fact.
Interpreting Your Scan Results: Open, Closed, or Filtered?
Once you run a port scan, the results will typically show one of three statuses for each port: open, closed, or filtered. Understanding what each of these means is, you know, key to taking appropriate action. An "open" port means that a service is actively listening on that port and is ready to accept connections. This could be a web server, an email server, or any other application that needs to communicate with the outside world. If it's an intended service, that's fine. If not, it's a red flag, honestly.
A "closed" port means that the port is accessible, but no application or service is listening on it. It's like a door that's there, but it's locked and no one is home. While a closed port isn't a direct vulnerability, it still responds to connection attempts, which could, you know, give some information to someone trying to map your network. Generally, you want ports that aren't in use to be closed, not open. This is a pretty straightforward status.
A "filtered" port indicates that a firewall or some other security device is blocking access to the port. This means the scanner couldn't determine if the port was open or closed because the firewall simply dropped the connection attempt. This is often a good thing from a security perspective, as it means your defenses are working to hide your ports from casual scans. However, it can also make troubleshooting harder if you're trying to get a service to work. It's a bit like a door that's not only locked but also hidden behind a very thick curtain, you know.
Test and verify servers, firewalls, and network perimeters with Nmap online. This tool provides the most accurate port status of a system's internet footprint. Getting these accurate results helps you make informed decisions about your network's safety. It's very important to regularly check these statuses, especially after making any changes to your network configuration or firewall rules. This proactive approach helps you stay ahead of potential issues, too.
Securing Your Network After a Scan: What to Do Next
Once you have the results of your port scan, the next step is to act on that information. If you find open ports that you didn't expect, or that are not needed, the first thing to consider is closing them. This often involves adjusting your firewall rules on your router or server. Unnecessary open ports are, you know, a common entry point for unwanted access, so reducing your network's exposed surface area is a very smart move. It's like making sure all your windows are shut if you're not using them, actually.
For ports that must remain open, it's absolutely vital to ensure the services running on them are up-to-date and properly secured. This means applying software updates, using strong passwords, and configuring services with the principle of "least privilege" – giving them only the access they need to function. Regularly checking for vulnerabilities associated with these services is also a very good practice. Our tools can help identify services, which is a good first step, you know.
If you're using port forwarding, the scan helps confirm if it's working as intended. If a port you forwarded isn't showing as open, you might need to recheck your router settings. Conversely, if a port is open that you didn't intend to forward, it's a sign to review your router's configuration for any accidental exposures. It's all about making sure your network behaves exactly how you want it to, more or less.
Regular port scanning should be part of your overall network security routine. The internet is constantly changing, and new vulnerabilities can emerge. By periodically scanning your network, you can catch new exposures quickly and address them before they become a problem. It's a continuous process, really, to maintain a safe online environment. This kind of consistent vigilance pays off, you know.
Common Questions About Port Scans
People often have questions about port scanning, and that's totally understandable. Here are some common ones, you know, that might be on your mind too:
Is a port scan illegal?
No, generally, performing a port scan on your own network or on a network you have explicit permission to scan is perfectly legal. It's a standard tool for network administrators and security professionals. However, scanning networks without permission can be considered a form of unauthorized access or a precursor to malicious activity, and that could, you know, lead to legal trouble. It's always best to stick to your own property or get clear permission, actually.
Can a port scan harm my computer?
A basic port scan, on its own, is unlikely to directly harm your computer or network. It's just sending out connection requests and observing responses. It's more of an information-gathering technique. However, very aggressive or poorly designed scans could, you know, sometimes cause minor network slowdowns or trigger intrusion detection systems. But the scan itself doesn't install anything or change your system settings. It's just knocking on doors, essentially.
How often should I scan my ports?
For home users, scanning your ports whenever you make significant changes to your network, like setting up new port forwarding rules or installing new network devices, is a good idea. For businesses, regular scheduled scans, perhaps monthly or quarterly, are a very smart practice. If you suspect any unusual network activity, an immediate scan is also, you know, highly recommended. Consistency is key here, really.
Taking Control of Your Network's Safety
Understanding and using a port scan is a fundamental step in managing your network's security and ensuring your services are accessible as intended. It gives you a clear picture of your network's exposure to the internet, allowing you to make informed decisions about your firewall rules and the security of your applications. By regularly checking for open ports and addressing any unexpected findings, you can significantly reduce your risk of unwanted access and potential vulnerabilities. It's a very proactive way to keep your digital space safe, you know.
Our port checker, based on reliable technology like Nmap, offers a straightforward way to perform these essential checks. It helps you quickly identify open and closed ports, verify port forwarding setups, and understand your network's perimeter. Taking a few minutes to run a scan can give you valuable insights and, honestly, peace of mind about your network's health. It's a simple tool with very powerful implications for your security, as a matter of fact.
So, why not take control of your network's safety today? Simply leverage our port checker to identify open and closed ports, ensuring your network is secure and your services are reachable only when you want them to be. It's a vital part of modern network management, and, you know, it's very accessible for everyone.

Port / Terminal Scan – Port Consultants Rotterdam

What Is Port Scanning and How Does It Work?
Port scan zenmap - designerstaia