Unraveling The Spanning-Tree Protocol: Keeping Your Network Smooth Today
Have you ever thought about what keeps a computer network running without a hitch, especially when there are many connections? It's almost like a city with many roads, where you want traffic to flow freely and not get stuck in endless circles. So, that's a bit like what the spanning-tree protocol does for our digital highways. It’s a foundational piece of network technology, really, and it helps prevent some big headaches that can pop up in a busy network, particularly on this day, May 17, 2024.
Without something like the spanning-tree protocol, or STP for short, our local area networks, or LANs, would face some serious trouble. We often design networks with extra connections, just in case one path fails. This redundancy is good for reliability, but it can also create a problem where data frames might just loop around and around, causing a huge mess. That's where STP steps in, actually, to make sure those extra paths work for us, not against us.
This article will help you get a better grip on the spanning-tree protocol. We will look at what it is, why networks truly need it, and how it manages to keep things orderly. You will also see how it has grown over time, from its first version to the more current ways it works. It’s a pretty clever system, you know, and we will explore its main ideas and how switches make their decisions.
Table of Contents
- What is Spanning-Tree Protocol (STP)?
- Why Do We Need STP? The Problem of Network Loops
- How STP Works: The Clever Way It Prevents Loops
- The Evolution of STP: Getting Faster and More Flexible
- Setting Up Spanning-Tree Protocol
- Frequently Asked Questions About Spanning-Tree Protocol
- Keeping Networks Steady
What is Spanning-Tree Protocol (STP)?
The spanning-tree protocol, often called STP, is a networking protocol that operates at Layer 2 of the OSI model, which is the data link layer. Basically, its main job is to stop what we call "bridge loops" from happening in a network. These loops can cause a lot of trouble, and STP was created, as my text says, to avoid the problems that arise when computers exchange data on a local area network, or LAN, that has these kinds of loops.
It’s a crucial tool, in some respects, for keeping networks reliable and stable. STP was first made official way back in 1990 by the IEEE standard 802.1d. This means it has been around for a good while, helping network folks manage their connections. The protocol works by making sure that even if you have many possible paths for data to travel, only one active path is used at any given moment, which is really quite clever.
Think of it like this: if you have two roads going to the same place, STP makes sure that only one is open for traffic at a time, but the other is ready to go if the first one closes. This way, you get the benefit of having a backup without the chaos of traffic going in circles. It truly is a system that brings order to potentially messy network designs, you know, especially with redundant links.
Why Do We Need STP? The Problem of Network Loops
So, why is STP so important? Well, it all comes down to something called "network loops." When you connect switches in a way that creates a circular path for data, you have a loop. While having extra paths, or redundancy, is good for making sure your network stays up if a link fails, it also creates the possibility of these loops. Without STP, these loops can cause two big problems, as my text explains: broadcast storms and MAC address table instability.
A broadcast storm happens when a broadcast frame, which is a message sent to everyone on the network, gets caught in a loop. It travels around and around, getting copied and resent endlessly. This, you know, very quickly floods the entire network with traffic, slowing everything down to a crawl or even bringing it to a complete halt. It's like a traffic jam that never ends, and it's something we definitely want to avoid.
The other issue is that switches learn where devices are by looking at their MAC addresses. In a loop, a switch might see the same MAC address coming from different ports, or even from the same port repeatedly. This confuses the switch, making its MAC address table unstable. As a matter of fact, it can lead to frames being sent to the wrong place, or just not getting to their destination at all, which is pretty bad for communication.
My text makes it clear that managing redundant paths is essential to prevent these broadcast storms and other related issues. STP is the key to having those helpful backup paths without suffering from the problems they can cause. It ensures network reliability and stability, which is, you know, absolutely vital for any organization today.
How STP Works: The Clever Way It Prevents Loops
The spanning-tree protocol works its magic by creating a single, logical path through a network, even if there are many physical paths. It does this by putting some switch ports into a "forwarding" state and others into a "blocking" state. A port in the forwarding state can send and receive data, while a port in the blocking state can only receive specific STP messages and will not forward regular data traffic. This is, in a way, how it stops the loops.
My text says that STP prevents the looping of frames by putting the interfaces of the switch in either forwarding or blocking state. The big question, then, is how does a switch figure out which interface should be in which state? This is where the protocol's clever design truly shines. It involves a process of election and decision-making among all the switches in the network. It's a bit like a democratic process, you know, but for network devices.
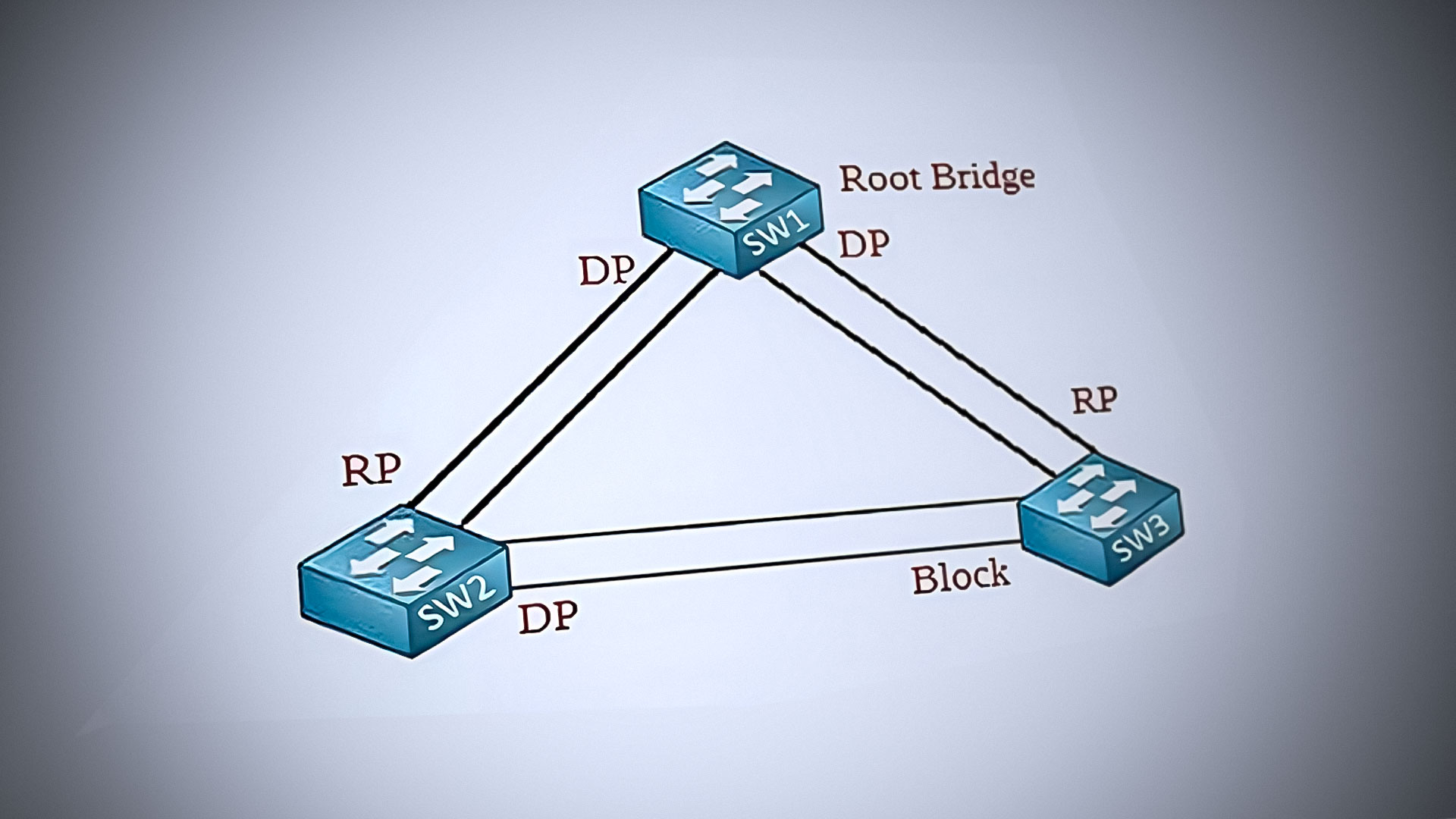
Electing a Root Bridge: The Network's Central Guide
The first step in how STP works is for all the switches in a Layer 2 domain to agree on one switch that will be the "root bridge." The root bridge is, essentially, the central point of the spanning tree. All other switches figure out their best path to this root bridge. My text explains that STP aims to resolve the loop problem by introducing this concept of the root bridge, and all bridges in the same Layer 2 domain will exchange information about it.
How is this root bridge chosen? Each switch has a unique identifier, often called a Bridge ID. This ID is made up of a priority value and the switch's MAC address. Switches send out special messages, which we will talk about soon, to tell each other their Bridge IDs. The switch with the lowest Bridge ID wins the election and becomes the root bridge. If two switches have the same priority, the one with the lowest MAC address wins, which is, you know, a pretty straightforward tie-breaker.
Once the root bridge is chosen, every other switch in the network will then calculate the shortest path to this root bridge. This path is called the "root path." The port on each non-root switch that leads to this shortest path is designated as its "root port." All root ports are put into a forwarding state, as a matter of fact, because they are part of the best way to get to the root bridge.
Port Roles: Forwarding and Blocking Traffic
After the root bridge is elected and root ports are determined, the switches then decide on the roles for all their other ports. Besides root ports, there are two other main port roles: designated ports and non-designated ports. Designated ports are also in a forwarding state, while non-designated ports are put into a blocking state.
A designated port is the port on a network segment (a connection between two switches or a switch and an end device) that has the best path to the root bridge for that particular segment. If two switches are connected, and neither port is a root port, they will compare their path costs to the root. The port on the switch with the better path cost becomes the designated port for that segment, and the other port becomes a non-designated port. This process ensures that, you know, only one port on any given segment is actively forwarding traffic.
My text says that to prevent loops, STP places some interfaces in a forwarding state and other interfaces in a blocking state. The ports in a blocking state are the non-designated ports. These ports are crucial because they provide the redundancy we want, but they don't actively forward data traffic, so they prevent loops. If an active link fails, STP can then quickly change a blocking port to a forwarding port, restoring connectivity. This mechanism is, quite frankly, what makes STP so powerful for network resilience.
BPDU Frames: Switches Talking to Each Other
How do switches exchange all this information about Bridge IDs, root paths, and port roles? They use special messages called Bridge Protocol Data Units, or BPDUs. My text mentions that a BPDU frame is a message sent from one switch to another. These BPDUs are, basically, the heartbeat of the spanning-tree protocol.
Switches regularly send BPDUs out of their ports. These messages contain information like the sending switch's Bridge ID, the root bridge's ID, and the cost to reach the root bridge. When a switch receives a BPDU, it compares the information in the BPDU with its own current understanding of the network. If it receives a BPDU that suggests a better path to the root bridge, or a better root bridge altogether, it will update its own information and potentially change its port roles. This continuous exchange of BPDUs allows the switches to, in a way, stay synchronized and react to changes in the network topology.
This constant communication is how switches detect loops and work together to prevent them. If a switch stops receiving BPDUs on a port that was previously forwarding, it might assume that link has failed and begin the process of unblocking a previously blocked port to restore connectivity. It's a very dynamic system, you know, always adapting to the network's current state.
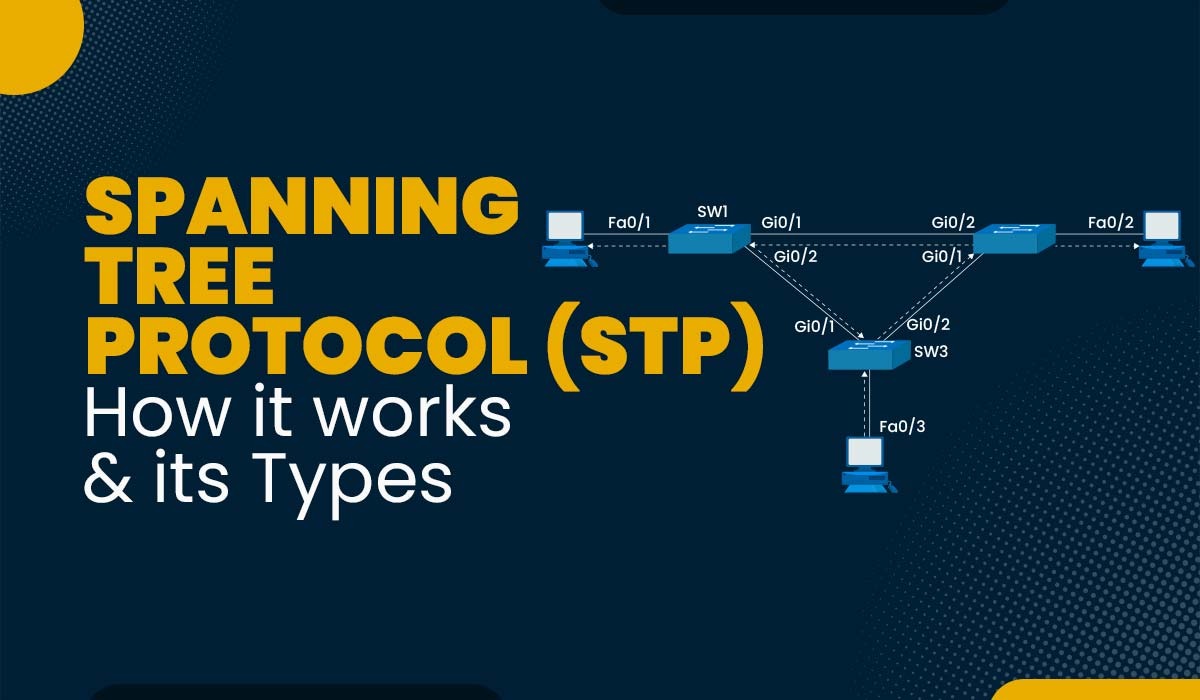
The Evolution of STP: Getting Faster and More Flexible
Since its beginning with IEEE 802.1d, the spanning-tree protocol has evolved quite a bit. My text mentions that STP has evolved into various forms to address different needs. The original STP, while effective at preventing loops, could be a bit slow to react when network changes happened, like a link going down. This slowness could lead to brief outages or packet loss. To fix this, newer versions were developed, which is, you know, a natural progression for any technology.
Rapid Spanning-Tree Protocol (RSTP)
One of the most significant improvements came with the Rapid Spanning-Tree Protocol, or RSTP, which is defined in IEEE 802.1w. My text points out that RSTP is an enhancement of the original STP, designed to provide faster convergence in a network topology. "Convergence" here means how quickly the network settles into a stable state after a change, like a link failing or a new switch being added.
RSTP achieves this faster convergence by introducing new port states and roles and by allowing switches to quickly agree on port roles without waiting for long timers to expire. For instance, RSTP can immediately put a port into a forwarding state if it's confident it won't create a loop. This is a big step up from the original STP, which, you know, often took 30-50 seconds to converge, causing noticeable delays. RSTP can often converge in just a few seconds, which is a very big difference for network performance.
Multiple Spanning-Tree Protocol (MSTP)
Another important evolution is the Multiple Spanning-Tree Protocol, or MSTP, which is defined in IEEE 802.1s. My text states that MSTP, also referred to as MST, supports multiple instances of spanning tree to efficiently channel VLAN traffic over different interfaces. This is particularly useful in larger, more complex networks that use Virtual LANs, or VLANs.
With original STP or RSTP, all VLANs in a network share the same spanning tree. This means that if one path is blocked by STP, it's blocked for all VLANs, even if you might want different VLANs to use different paths for better load sharing. MSTP solves this by allowing you to create multiple spanning-tree instances. Each instance can have its own root bridge and its own set of forwarding and blocking ports. This means, in a way, you can optimize traffic flow for different groups of devices, which is very helpful for network efficiency.
For example, you could configure one spanning-tree instance to make VLAN 10 traffic use one set of links, and another instance to make VLAN 20 traffic use a different set of links. This allows for more flexible and efficient use of redundant links, which is, you know, a pretty advanced feature for bigger networks.
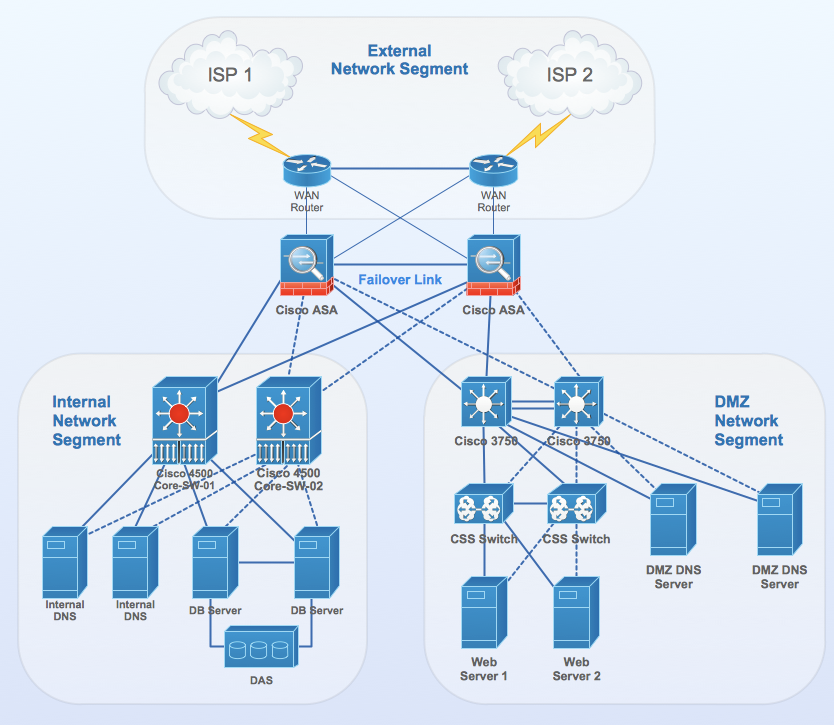
Setting Up Spanning-Tree Protocol
Configuring and verifying the spanning-tree protocol on network devices, especially switches, is a common task for network administrators. My text mentions learning how to configure and verify STP on Cisco switches with examples and commands. While the specific commands vary between different vendors, the basic principles remain the same. The goal is always to ensure STP is running correctly to prevent loops and provide redundancy.
Typically, you would enable STP globally on a switch, or it might be enabled by default. Then, you might adjust parameters like the switch's priority to influence which switch becomes the root bridge. For instance, you usually want a core switch, or a very stable switch, to be your root bridge. You can also configure specific port settings, such as port cost, to influence which paths STP considers best. These configurations help, you know, fine-tune the spanning tree to match your network design.
It's also important to verify that STP is working as expected. This involves checking which switch is the root bridge, what roles your ports have (root, designated, or blocking), and that no unwanted loops are forming. Tools and commands are available on switches to show you the current STP status, which is very helpful for troubleshooting. Understanding these outputs is key to ensuring your network remains stable and performs well.
Frequently Asked Questions About Spanning-Tree Protocol
What is the main purpose of Spanning Tree Protocol?
The main purpose of the spanning-tree protocol is to prevent bridge loops in a network and to stop the broadcast storms that happen because of those loops. It also helps manage redundant paths, making sure the network stays reliable if a link or switch fails, which is, you know, pretty important for network uptime.
How does STP prevent loops?
STP prevents loops by putting some switch ports into a "forwarding" state and other ports into a "blocking" state. It does this by first electing a root bridge and then calculating the best paths to that root bridge. Any redundant paths that would create a loop are then put into a blocking state, so they don't forward regular data traffic. This way, only one active path exists for any given destination, which is, you know, how it keeps things orderly.
What are the different types of STP?
The original spanning-tree protocol is defined by IEEE 802.1d. However, it has evolved into more advanced forms. The main types you will hear about are Rapid Spanning-Tree Protocol (RSTP), which offers faster network convergence, and Multiple Spanning-Tree Protocol (MSTP), which allows for multiple spanning-tree instances to manage VLAN traffic more efficiently. CST is also an implementation of STP, as my text points out. You can learn more about network protocols on our site, and for more details on Layer 2 technologies, check out this page.
Keeping Networks Steady
The spanning-tree protocol is, truly, a quiet hero of network stability. It works behind the scenes, making sure our redundant network connections provide reliability without causing chaos. From its early days as IEEE 802.1d to its more advanced forms like RSTP and MSTP, it continues to be a fundamental part of keeping local area networks running smoothly. My text shows that it is essential to manage redundant paths in a network to prevent broadcast storms and other issues. This protocol ensures that your data has a clear, loop-free path to follow, which is, you know, something we all rely on every single day.
What is Spanning Tree Protocol (STP) and how it works?
Introduction to the Spanning Tree Protocol – Expert Network Consultant
What is Spanning Tree Protocol (STP) and How it works?