Mastering EC2 Security: How To Change Security Group Settings For Your Instances
Managing your cloud resources effectively means keeping a close watch on who and what can talk to your virtual servers. This is where the ability to change security group settings for your EC2 instances becomes incredibly important. Think of it as adjusting the digital doors and windows for your applications. Knowing how to handle these changes with confidence is a skill every cloud user needs to have, so you can keep your systems safe and running smoothly.
Amazon Elastic Compute Cloud, or Amazon EC2 for short, offers a very wide and deep compute platform, with a great selection of instances and choices for processors, storage, and networking, you know. It's a service from Amazon Web Services (AWS) that provides cloud-hosted virtual machines, which are called instances, to run all sorts of applications. Using Amazon EC2 helps reduce hardware costs, too, which is a pretty big deal for many businesses.
These instances are really virtual servers, they are run on Amazon's huge infrastructure, and they are fully customizable, so you can configure them in many ways. But what protects these virtual machines? That's where security groups come into the picture, acting like virtual firewalls. Understanding how to manage these groups, especially when you need to change security group rules, is a fundamental part of keeping your cloud setup secure and operational, so let's get into it.
Table of Contents
- What Are EC2 Instances and Security Groups, Anyway?
- Why Would You Need to Change an EC2 Security Group?
- The Good News: You Can Change Security Groups on Running EC2 Instances!
- How to Change Security Group Settings: A Step-by-Step Guide
- Things to Keep in Mind When You Change Security Groups
- Common Scenarios for Changing Security Groups
- Best Practices for Managing EC2 Security Groups
- Troubleshooting Tips for Security Group Changes
- Frequently Asked Questions About EC2 Security Groups
What Are EC2 Instances and Security Groups, Anyway?
Before we get into the specifics of how to change security group rules, it's good to have a solid grasp of what we're actually talking about. Amazon EC2 is, you know, a core part of AWS. It lets you rent servers offsite, which are located in Amazon’s global data centers. This setup really helps reduce hardware costs for many organizations, which is a pretty sweet deal.
EC2 stands for Elastic Compute Cloud. It's a service that gives you virtual servers, or "instances," that run on Amazon's infrastructure. These instances are very customizable, and you can configure them with a wide variety of settings. They are, in a way, the backbone for many cloud-based applications, providing the compute power you need.
EC2 Instances: Your Virtual Machines
Basically, an EC2 instance is your virtual computer in the cloud. You can boot an Amazon Machine Image (AMI) to set up one of these virtual machines, which Amazon manages. This makes it easier to deploy applications in a way that can grow with your needs. You get to choose from over 750 instance types, with the latest processors, storage, and networking options, so there's a lot of flexibility there.
These instances are where your applications live and run. They are like the individual offices in a large building. Each office needs some kind of protection, you see. That protection, in the cloud world, comes from security groups, which is what we are focusing on today.
Security Groups: The Digital Bouncers
A security group acts as a virtual firewall for your EC2 instances. It controls both inbound and outbound traffic, so it decides who can talk to your instance and what your instance can talk to. When you launch an instance, you associate one or more security groups with it, which is rather important.
These groups contain rules that permit traffic. For example, you might have a rule that allows web traffic (port 80 and 443) from anywhere, but SSH access (port 22) only from your office IP address. Without the right rules, your applications might not work, or worse, they could be open to unwanted access, which nobody wants, really.
Why Would You Need to Change an EC2 Security Group?
Life in the cloud is pretty dynamic, and your security needs can shift quite a bit. There are several common reasons why you might find yourself needing to change security group settings for your EC2 instances. It's not just a set-it-and-forget-it kind of thing, you know.
Opening Up New Connections
Maybe you're deploying a new application that needs to use a different port, or you've added a new service that requires specific inbound access. For instance, if you just set up a database server on your EC2 instance, you'll need to open the database port, like 3306 for MySQL, to other instances or specific IP addresses. This is a very common scenario, actually.
Another reason could be expanding access for a team member or a new office location. You might need to add their IP address to allow SSH or RDP access. These changes are about enabling necessary communication, so your systems can function as intended.
Tightening Down Security
On the flip side, you might need to make your security tighter. Perhaps a project has ended, and you no longer need a certain port open, or you've identified an IP address that should no longer have access. Removing unnecessary rules is just as important as adding new ones, maybe even more so.
Regular security audits often reveal rules that are too broad, like allowing SSH from "0.0.0.0/0" (which means anywhere on the internet). Changing this to a more specific IP range significantly reduces your exposure. It's about reducing the attack surface, you see, which is always a good idea.
Troubleshooting Connectivity Puzzles
Sometimes, applications just don't talk to each other, and you can't figure out why. Often, the culprit is a security group rule that's blocking the traffic. Temporarily adjusting a rule, or adding a new one, can help you diagnose connectivity problems. Just remember to revert or refine those rules once you've found the issue, which is pretty important.
This diagnostic step is a bit like checking if a door is locked when someone can't get into a room. You might open it briefly to see if that fixes the problem, then re-lock it with the right key. It's a practical, hands-on way to solve network issues, so it's a skill worth having.
The Good News: You Can Change Security Groups on Running EC2 Instances!
One of the really helpful features of AWS EC2 is that you don't have to stop or restart your instance to change its associated security groups. This is a big deal, actually, as it means you can adjust your network access rules without causing downtime for your applications. The changes usually take effect almost immediately, which is super convenient.
This flexibility allows for quick responses to security needs or operational changes. Whether you're reacting to a potential threat or enabling a new feature, you can make these adjustments without disrupting your users. It's a pretty powerful capability, you know, that helps keep things moving.
How to Change Security Group Settings: A Step-by-Step Guide
There are a few ways to go about changing security groups for your EC2 instances. The most common methods involve using the AWS Management Console or the AWS Command Line Interface (CLI). Both approaches get the job done, but they suit different preferences and automation needs, so let's look at them.
Using the AWS Management Console
The console provides a graphical interface, which is often the easiest way for many people to make changes. It's pretty intuitive, especially if you're just starting out with AWS. You can click your way through the steps, which is nice.
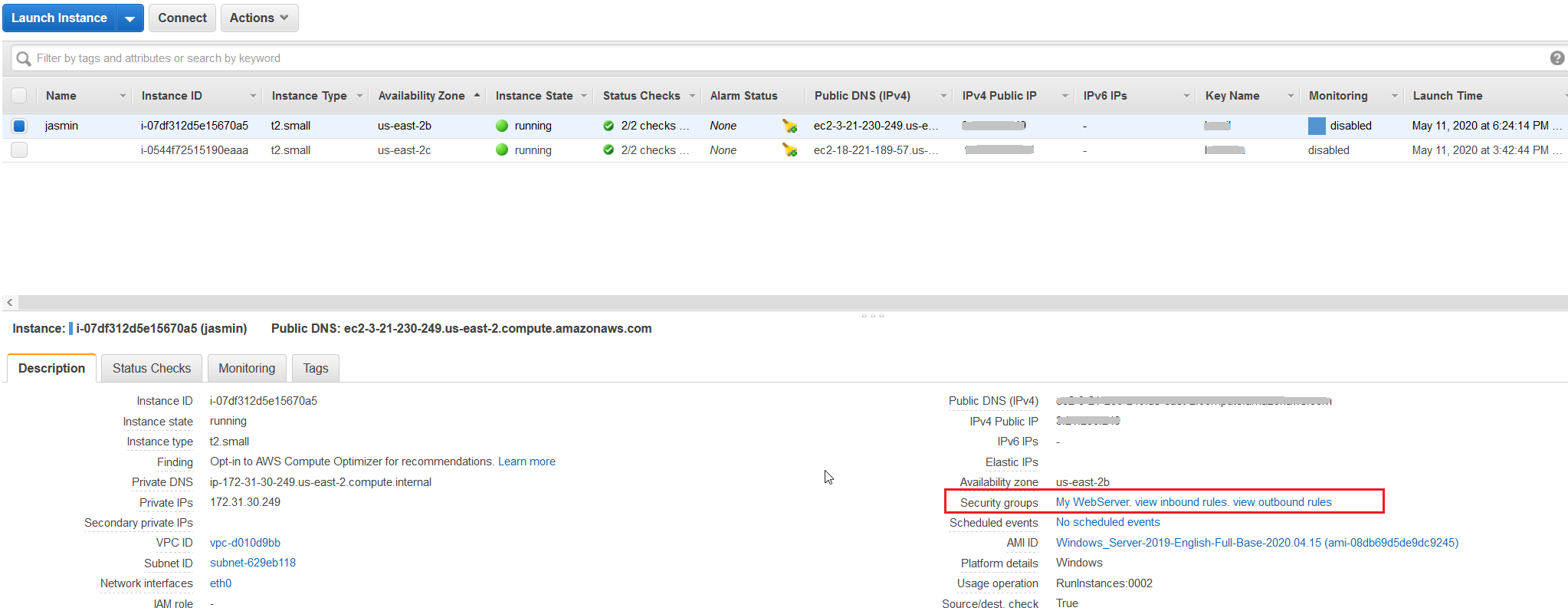
Finding Your Instance
- Log in to the AWS Management Console: Go to the AWS website and sign in.
- Navigate to EC2 Dashboard: Find "EC2" in the services menu and click on it. You'll land on the EC2 Dashboard.
- Select Your Instance: In the left-hand navigation pane, click "Instances." You'll see a list of all your running EC2 instances. Find the one you want to modify and click on its ID to select it.
Modifying Security Groups
- Access Security Settings: With your instance selected, look at the "Actions" dropdown menu.
- Choose Networking: Hover over "Networking," then click on "Change Security Groups."
- Select New Security Groups: A new window will appear, showing the security groups currently associated with your instance. You can remove existing ones by clicking the "x" next to them and add new ones by selecting them from the dropdown list.
- Apply Changes: Once you've made your selections, click "Save." The changes should take effect very quickly, which is rather handy.
Using the AWS Command Line Interface (CLI)
For those who prefer working with text commands or want to automate changes, the AWS CLI is a very powerful tool. It allows you to script these actions, which can save a lot of time if you have many instances or frequent changes. It's a bit more technical, but very efficient.
Setting Up Your CLI
First, you'll need to have the AWS CLI installed and configured on your local machine. This involves installing the software and then setting up your AWS credentials, so the CLI knows who you are and what permissions you have. There are plenty of guides online for this setup, you know, it's pretty standard.
The `modify-instance-attribute` Command
To change security groups using the CLI, you'll use the `aws ec2 modify-instance-attribute` command. Here's a basic example of how it works:
aws ec2 modify-instance-attribute \ --instance-id i-0abcdef1234567890 \ --groups sg-0123456789abcdef0 sg-0fedcba9876543210 In this command:
- `--instance-id` is the unique identifier for your EC2 instance.
- `--groups` is where you list the IDs of the security groups you want to associate with the instance. You need to provide the full list of security groups you want the instance to have, as this command replaces the existing ones.
It's important to remember that this command replaces *all* existing security groups with the ones you list. So, if you want to keep some and add others, you must include the IDs of the ones you want to keep in your list, too. This is a common point of confusion, so be careful.
Using AWS SDKs (Brief Mention)
For developers, AWS provides Software Development Kits (SDKs) in various programming languages like Python (Boto3), Java, Node.js, and more. These SDKs allow you to programmatically manage your AWS resources, including changing security groups, as a matter of fact. This is the ultimate level of automation and integration for your applications, so it's very powerful for building custom tools.
Things to Keep in Mind When You Change Security Groups
Changing security groups is a pretty straightforward process, but there are a few important considerations to keep in mind to avoid unexpected issues. Being aware of these points can save you some headaches, which is always a good thing.
Immediate Impact
As mentioned, changes to security groups take effect almost instantly. This means if you remove a rule that's essential for your application, connectivity will stop right away. Likewise, if you add a rule, the new access becomes available immediately. This immediate effect can be both a blessing and a bit of a challenge, you know, so be prepared.
Always double-check your changes before applying them, especially in a production environment. A quick mistake could lead to downtime, which is something everyone wants to avoid. It's a bit like making changes to a live network, you see, so caution is important.
Least Privilege Principle
A fundamental security concept is the principle of least privilege. This means you should only grant the minimum permissions necessary for a task or service to function. When you change security group rules, always try to be as specific as possible with IP addresses and port ranges. Avoid opening ports to "0.0.0.0/0" (everyone) unless it's absolutely necessary, like for a public web server, and even then, consider other layers of protection, too.
For example, if only your development team needs SSH access, specify their office IP range rather than opening port 22 to the entire internet. This greatly reduces your exposure to potential attacks, which is a pretty smart move.
Testing, Testing, Testing
After making any changes to your security groups, it's a very good idea to test the connectivity. Try to access your application or instance

Preparing for Change: Security - The MPI Group

How to attach or change a security group on an EC2 instance – Seecoding
How to Move AWS EC2 instance to another Security Group?