Pam Bardot: Keeping Your Digital Doors Safe
In our fast-moving digital world, keeping important information secure is, well, pretty much everything. Every day, it seems like new threats pop up, making us all think harder about how we protect our most sensitive stuff. That's why we're going to talk about something really important today, something we're calling "Pam Bardot." It's a way of looking at security that helps guard your digital spaces.
You know, it's a bit like having a very careful doorman for your most exclusive digital rooms. This Pam Bardot idea focuses on managing who gets to do what with your most valuable digital assets. It's about making sure only the right people have the keys to the kingdom, and even then, only for the time they really need them, which is kind of smart, right?
So, what we're talking about here isn't just a fancy term; it's a crucial approach to staying safe online. It helps organizations, big and small, stand strong against cyber threats. We will, in some respects, explore how this particular method, this "Pam Bardot," keeps things locked down, watched over, and protected from those who shouldn't be poking around.
Table of Contents
- What Exactly is Pam Bardot?
- Why Pam Bardot Matters So Much Today
- How Pam Bardot Works: A Closer View
- Pam Bardot in Action: Real-World Scenarios
- Common Questions About Pam Bardot
- Securing Your Future with Pam Bardot
What Exactly is Pam Bardot?
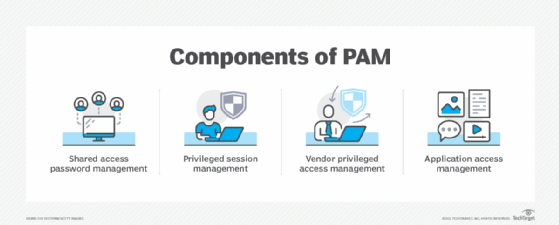
When we talk about Pam Bardot, we are really talking about Privileged Access Management, or PAM for short. It's an identity security solution, basically a smart system, that helps keep organizations safe from cyber threats. This system works by watching, finding, and stopping any unauthorized "privileged" access, which is pretty important, actually.
You see, Pam Bardot, as a cybersecurity strategy, includes specific technologies. These are for taking charge of the elevated access and permissions that certain identities and users have. Think of it like this: some people in an organization need extra access to do their jobs, but that extra access also comes with extra risk, you know?
So, in essence, Pam Bardot is a part of identity management and a branch of cybersecurity. Its main focus is on controlling, watching, and keeping safe those special "privileged accounts" inside an organization. It's about making sure that these powerful accounts, which could cause a lot of trouble if misused, are handled with the utmost care, in a way.
Why Pam Bardot Matters So Much Today
The digital world, as we know, is always changing. With more and more information stored online, the need for solid security has never been greater. Pam Bardot is, in fact, a crucial cybersecurity strategy and a collection of technologies. It aims at protecting an organization’s most sensitive data and critical systems by really controlling and watching over everything.
Consider, for instance, the kind of things that can happen when privileged access isn't properly managed. A breach of a single privileged account could let someone get into all sorts of important systems. This could lead to data theft, system damage, or even a complete shutdown, which is, obviously, a big problem.
Pam Bardot helps stop these kinds of problems before they even start. By keeping a close eye on who has access to what, and making sure that access is only granted when truly needed, it significantly lowers the risk. This protection is, arguably, more vital now than ever before, given the constant attacks we hear about.
How Pam Bardot Works: A Closer View
Pam Bardot doesn't just sit there; it's an active system. It involves several key steps to make sure privileged access is handled correctly. This process helps organizations maintain a strong security posture, which is a good thing.
First off, it identifies what "privileged access" even means within a specific system. This could be anything from an administrator account to a service account that runs important applications. Once identified, these accounts get special treatment, you know, a bit like VIPs but with more security around them.
Then, Pam Bardot sets up rules for how these accounts can be used. Who can access them? When? For how long? What actions can they perform? These questions are all answered and enforced by the system. It's about creating a very clear set of boundaries, which, honestly, makes a lot of sense.
Monitoring and Control
A big part of Pam Bardot is the constant watching and control. It's not enough to just set rules; you have to make sure those rules are being followed. This means monitoring all activity related to privileged accounts, literally every single action.
If someone tries to access a system they shouldn't, or tries to do something outside their permissions, Pam Bardot detects it. It can then, quite literally, prevent that action from happening. This real-time detection and prevention is what makes it such a powerful tool against unauthorized access, which is pretty cool.
The system also keeps detailed records of all privileged activities. This is useful for auditing and forensic investigations, should something go wrong. Knowing exactly who did what, and when, is invaluable for understanding security incidents and preventing them in the future, as a matter of fact.
Protecting Sensitive Data
At its core, Pam Bardot is about safeguarding an organization's most sensitive data and critical systems. This includes financial records, customer information, intellectual property, and other valuable assets. Losing this kind of data can have huge consequences, financially and reputationally, you know?
By controlling privileged access, Pam Bardot makes it much harder for cybercriminals to get their hands on this sensitive information. Even if they manage to get past some initial defenses, the layers of control around privileged accounts act as a strong barrier. It's like having a very secure vault inside another secure vault, which is rather effective.
This approach helps ensure that critical systems, the ones that keep an organization running, remain operational and secure. It's about peace of mind, really, knowing that your most important digital assets are under constant guard. Learn more about privileged access management on our site.
Pam Bardot in Action: Real-World Scenarios
To really get a feel for Pam Bardot, let's think about some everyday situations where it makes a big difference. Imagine a large energy company, for instance, like Oncor Electric Delivery. They have complex systems that manage power grids and customer accounts, and these systems need constant protection.
Oncor, for example, needs to ensure that only authorized personnel can access their critical infrastructure controls. Pam Bardot would help them control who can log in to those systems, when they can, and what specific changes they are allowed to make. This prevents unauthorized access that could lead to widespread power outages or other serious issues, which is something we all want to avoid, right?
Similarly, consider how Oncor manages power restoration during a winter storm. Damage assessment and vegetation management teams need access to specific tools and information. Pam Bardot ensures that these teams have the necessary elevated permissions for their tasks, but only for the duration needed and only for the specific tools required. This minimizes risk while still allowing important work to get done efficiently, which is pretty smart, honestly.
Even for something like managing customer accounts or energy efficiency programs, Pam Bardot plays a role. It helps secure access to sensitive customer data and billing systems. This ensures that only authorized employees can view or modify customer information, protecting privacy and preventing fraud, which is, obviously, very important for trust. You can also sign in to access Oncor Electric Delivery services and manage your account securely.
Common Questions About Pam Bardot
People often have questions when they first hear about something like Pam Bardot. Here are a few common ones, kind of like what you might find in a "People Also Ask" section, you know?
What makes Pam Bardot so important for cybersecurity?
Pam Bardot is really important because it tackles one of the biggest weak spots in security: privileged accounts. These accounts, with their elevated permissions, are prime targets for cyber attackers. By strictly controlling and monitoring them, Pam Bardot significantly reduces the chances of a major breach. It's like having a very strong lock on your most valuable possessions, which is, arguably, a good idea.
How does Pam Bardot actually prevent unauthorized access?
It prevents unauthorized access in a few ways, actually. It enforces strong authentication for privileged users, meaning they have to prove who they are very carefully. Then, it limits their access to only what they need, for only as long as they need it. Plus, it constantly watches all their activities, so any suspicious behavior is flagged and stopped immediately. This multi-layered approach is very effective, you know.
What kinds of accounts does Pam Bardot typically protect?
Pam Bardot usually protects accounts with high-level permissions. This includes things like administrator accounts, root accounts, service accounts that run applications, and even emergency access accounts. Basically, any account that has the potential to make big changes or access very sensitive data falls under its watchful eye. It's about protecting the keys to the kingdom, in a way.
Securing Your Future with Pam Bardot
As we move forward in this digital age, the need for strong security solutions like Pam Bardot will only grow. It's not just about stopping attacks; it's about building a resilient and trustworthy digital environment. By focusing on managing privileged access, organizations can really strengthen their defenses and protect what matters most.
Implementing Pam Bardot means taking a serious, proactive step towards a safer digital future. It means understanding that not all access is equal, and that the most powerful access needs the most careful handling. This approach is, frankly, a smart investment in an organization's long-term security and stability, you know?
So, whether you're thinking about your own organization or just curious about how modern cybersecurity works, remembering the principles of Pam Bardot can give you a better grasp. It's about making informed choices to keep our digital world a little safer, today and well into the future. For more information on cybersecurity best practices, you might find this article on CISA's cybersecurity best practices helpful.
What is privileged access management (PAM)? (2022)

🔐 Privileged Access Management (PAM): The Backbone of Modern Cybersecurity

PAM Academy - We're excited to announce that our Part 3... | Facebook